The 2026 Guide to Anonymous Torrenting: Six Layers Between You and a DMCA Notice
Last updated: February 14, 2026 | TorrentGalaxy OPSEC Series
Every time you click a magnet link, you join a swarm — a public network where every peer can see your IP address. That IP connects to your ISP account, your name, and your physical address. Without protection, you are broadcasting your identity to everyone sharing the same file, including the automated monitoring bots that copyright trolls use to harvest IPs at industrial scale.
This guide is the central resource for the TorrentGalaxy OPSEC series. It covers the complete protection stack — not just “get a VPN” — organized as six progressive layers. Each layer eliminates a specific attack vector. Skip one, and you leave a gap that monitoring companies, ISPs, or malicious actors can exploit.
⚡ The 30-Second OPSEC Checklist
If you’re in a hurry, here’s the entire guide compressed into six steps. Each links to the full section below.
- VPN on P2P server — WireGuard protocol, no-logs provider, ideally with Post-Quantum Encryption (Layer 1)
- Bind your torrent client to the VPN adapter — This is the step most guides skip. It’s more important than a kill switch. (Layer 2)
- Test for DNS leaks — Visit ipleak.net and confirm all DNS servers belong to your VPN, not your ISP (Layer 3)
- Block WebRTC in your browser — Disable it in Firefox (
about:config) or install uBlock Origin on Chrome (Layer 4) - Enable VPN port forwarding — Essential if your ISP uses CGNAT. Disable UPnP/NAT-PMP in your torrent client. (Layer 5)
- Run uBlock Origin + VPN DNS blocker — Two layers of ad/malware protection for torrent sites (Layer 6)
Then run the Total Failure Test once to verify everything works.
The Six-Layer Protection Stack
| Layer | What It Does | Threat It Eliminates | Priority |
|---|---|---|---|
| 1. VPN | Encrypts traffic, replaces your IP | Copyright trolls, ISP surveillance, throttling | 🔴 Mandatory |
| 2. Interface Binding | Restricts torrent client to VPN adapter only | IP leaks during VPN disconnections | 🔴 Critical |
| 3. DNS Leak Protection | Routes DNS queries through VPN tunnel | ISP sees which sites/trackers you visit | 🟡 Important |
| 4. WebRTC Block | Disables browser API that exposes real IP | Malicious scripts on torrent sites | 🟡 Important |
| 5. Port Forwarding | Opens VPN port for incoming peer connections | Slow speeds, CGNAT blocking | 🟢 Performance |
| 6. Browser Hardening | Blocks malicious ads, tracking scripts, miners | Malware, phishing, crypto miners | 🟢 Defense-in-depth |
Each layer is independent. Layer 1 alone provides basic protection. Layers 1+2 provide strong protection. All six together provide comprehensive anonymity.
The Threat Model: Who Is Watching and How
Before you can protect yourself, you need to understand who is actually looking at your torrent activity and what tools they use. There are four distinct adversaries, and each one exploits a different piece of information.
1. Copyright Trolls (Swarm Monitoring)
These are the most active threat to everyday torrent users. Companies like Maverickeye (Germany), Guardaley (UK/Germany), and MarkMonitor join torrent swarms the same way you do. They connect to the tracker, join the peer list, and run automated scripts that log every IP address they see — along with timestamps, the torrent’s infohash, and download/upload activity.
Their business model isn’t prosecution. It’s settlement extraction. They take logged IPs, match them to ISPs via WHOIS databases, subpoena the ISP for the subscriber name behind the IP, and send demand letters — typically $1,000–$3,000 — threatening a lawsuit unless you pay. A Danish court in 2021 charged law firm Njord Law and its partners with fraud after it emerged that their monitoring partners (CMS/MIRCOM, both Guardaley affiliates) didn’t even hold the copyrights to the works they were enforcing. Tens of thousands of subscribers across Scandinavia had already paid settlements before the scheme collapsed.
A U.S. court went further: a federal judge in Washington state issued a devastating order questioning whether Maverickeye’s tracking expert (Benjamin Perino) was qualified at all, noting his credentials consisted of “a technical high school education and work experience unrelated to peer-to-peer file-sharing technology.” The court also raised doubts about whether one of Maverickeye’s key witnesses actually existed — requesting “proof beyond a reasonable doubt of Arheidt’s existence.”
The entire chain depends on one thing: your real IP address appearing in the swarm.
2. Your ISP (Traffic Analysis)
Your Internet Service Provider sees every connection your device makes. Without encryption, they can identify BitTorrent protocol headers, see which trackers you connect to, and read the filenames in the torrent metadata. Even with encryption, if you’re connecting directly to known tracker IPs, your ISP can infer what you’re doing.
ISPs use this information in three ways: throttling your P2P bandwidth using Deep Packet Inspection (DPI), forwarding copyright notices they receive from monitoring companies, and in some jurisdictions, proactively reporting subscribers to rights holders under “graduated response” (three-strike or six-strike) systems.
3. Malicious Peers (Data Harvesting)
Not every peer in a swarm is downloading a movie. Some are harvesting data. They collect IP addresses paired with specific content infohashes, building databases they sell to advertising networks, data brokers, or law enforcement agencies. Others use your IP to launch targeted attacks — port scanning, DDoS, or attempting to exploit known vulnerabilities on your home network.
4. Malicious Websites (Browser Exploits)
Torrent sites — including TorrentGalaxy — serve third-party advertisements. Some of these ads contain malicious JavaScript: cryptominers that hijack your CPU, “click-fix” phishing prompts, fake codec installers that are actually trojans, and redirect chains that drop tracking cookies or attempt drive-by downloads. This threat operates in your browser, not your torrent client, but it’s part of the same activity session.
For a deep dive on verifying sites and scanning downloads, see our TorrentGalaxy Safety Guide.
Layer 1: VPN — The Foundation (Mandatory)
A VPN is the single most important protection for torrenting. It replaces your real IP address with the VPN server’s IP in every peer connection, encrypts all traffic so your ISP can’t see what you’re doing, and groups your activity with hundreds of other users behind the same shared IP — making it statistically impossible to attribute a specific download to a specific person.
This is the one layer you cannot skip. Everything else in this guide adds depth, but without a VPN, you’re exposed to all four adversaries simultaneously.
What a VPN Actually Does for P2P
There are three distinct protection mechanisms at work, and understanding each one tells you what specific threat it neutralizes:
Encryption hides the content of your traffic. Your ISP sees data flowing to a VPN server’s IP address but cannot identify it as BitTorrent traffic. This defeats DPI-based bandwidth throttling and prevents your ISP from reading filenames, tracker URLs, or protocol headers.
Tunneling hides the destination of your traffic. Instead of your device making hundreds of direct connections to peers in the swarm, all traffic flows through a single encrypted tunnel to the VPN server. The VPN server then connects to the swarm on your behalf. Your ISP sees one connection; the swarm sees the VPN server’s IP.
Shared IP addresses provide deniability. Hundreds of users connect simultaneously to the same VPN server. If a monitoring bot logs that server’s IP in a swarm, that IP address corresponds to hundreds of different people — not just you. Combined with a verified no-logs policy (meaning the VPN provider cannot identify which user was assigned which IP at any given time), the chain from IP address to individual subscriber is permanently broken.
For the complete technical breakdown of encryption protocols, tunneling overhead, and shared IP mechanics, see our VPN for Torrenting Survival Guide.
Protocol Comparison: What to Use in 2026
| Protocol | 2026 Status | Encryption | Speed Impact | Battery (Mobile, 4hr) | Best For |
|---|---|---|---|---|---|
| WireGuard | Industry standard | ChaCha20-Poly1305 | 3–8% loss | ~4–5% drain | Torrenting (default choice) |
| OpenVPN UDP | Legacy / fallback | AES-256-GCM | 10–20% loss | ~12–18% drain | Bypassing firewalls (obfuscation support) |
| OpenVPN TCP | Specialized | AES-256-GCM | 15–25% loss | ~15–20% drain | Restrictive networks (port 443 mimics HTTPS) |
| IKEv2/IPSec | Mobile optimized | AES-256 | 5–12% loss | ~8–10% drain | Mobile network switching (Wi-Fi ↔ cellular) |
For torrenting, use WireGuard. It’s the fastest protocol, uses the least battery on mobile, and handles network transitions (Wi-Fi to cellular) without dropping the tunnel. OpenVPN is only necessary if WireGuard is actively blocked on your network (some corporate firewalls and ISPs in restrictive countries target its traffic patterns).
Post-Quantum Encryption: Future-Proofing Layer 1
By 2026, “post-quantum encryption” has moved from niche concern to marketing standard. Here’s what matters: current VPN handshakes use public-key algorithms (RSA, ECDH) that quantum computers will eventually be able to break. The threat isn’t that someone can decrypt your VPN today — they can’t. The threat is “harvest now, decrypt later”: an adversary records your encrypted VPN traffic today and stores it, planning to decrypt it when quantum hardware matures.
Post-Quantum Encryption (PQE) replaces vulnerable key exchange algorithms with quantum-resistant alternatives (ML-KEM, formerly CRYSTALS-Kyber). Three VPNs have deployed it as of early 2026:
- NordVPN — NordLynx is quantum-secure on all platforms (live)
- ExpressVPN — ML-KEM integrated into Lightway protocol since January 2025 (live)
- Mullvad — Post-quantum WireGuard on all platforms (live)
- ProtonVPN — New architecture with PQE planned for 2026 rollout (in development)
For torrenting specifically, PQE is low-priority. The contents of your torrent swarm traffic are the files themselves, which are publicly available to every peer. An attacker wouldn’t gain anything by decrypting your VPN tunnel years later. But PQE is a strong signal that a VPN provider takes long-term security seriously — and it costs you nothing in performance (the quantum-resistant handshake adds a few bytes, zero throughput impact).
For the full PQE breakdown including testing results, see our Best VPNs for Android Torrenting.
Choosing a VPN: The Five Non-Negotiables
Not every VPN is suitable for P2P. The budget VPN you use for Netflix geo-unblocking might actively block BitTorrent traffic or, worse, log your activity. Here are the five features that separate a real torrenting VPN from marketing noise:
1. Verified no-logs policy. The VPN must have undergone an independent security audit (by firms like Securitum, Cure53, or Deloitte) confirming they store zero connection logs. Court-tested is even better — Mullvad’s servers were physically seized by Swedish police in 2023 and contained no user data. “We don’t keep logs” on a marketing page means nothing without independent verification.
2. P2P-allowed servers. Some VPNs allow torrenting on all servers; others restrict it to specific P2P-optimized nodes. Either works, but you need to confirm before downloading. Attempting to torrent on a non-P2P server typically results in the VPN silently blocking tracker connections — you’ll see “stalled” or “no seeds found” without understanding why.
3. WireGuard protocol support. Covered in the protocol table above. WireGuard is the only protocol worth using for sustained P2P transfers in 2026 unless you have a specific reason to need OpenVPN’s obfuscation capabilities.
4. Kill switch. If the VPN connection drops — server maintenance, network interruption, router restart — your device will revert to your real IP address unless something stops it. A kill switch blocks all internet traffic when the VPN tunnel is down. It’s a safety net for the brief moment between disconnection and your reaction. (Layer 2 covers a more reliable alternative, but the kill switch is still essential as a baseline for non-torrent traffic.)
5. Favorable jurisdiction. Where the VPN company is incorporated determines which government can legally compel them to hand over data. Switzerland (ProtonVPN), Panama (NordVPN), Sweden (Mullvad), and the British Virgin Islands (ExpressVPN) have strong privacy laws and no mandatory data retention. VPNs based in the US, UK, or Australia operate under Five Eyes surveillance agreements and can be served with secret court orders. Jurisdiction matters most when a no-logs claim hasn’t been independently verified.
Our Recommendations
ProtonVPN is our primary recommendation for most users. Swiss jurisdiction, audited no-logs policy, native port forwarding on all platforms (critical for Layer 5), WireGuard support, and NetShield DNS-level blocking. It’s the best all-around package for torrenting.
Mullvad is the alternative for privacy purists. No email required to sign up — you generate an anonymous account number. Accepts cash payment by mail (no payment trail at all). Post-quantum encryption already live. Court-tested when Swedish police seized their servers and found nothing. The tradeoff: no port forwarding, no mobile app as polished as ProtonVPN’s, and slightly smaller server network.
For Android-specific VPN recommendations with installation walkthroughs, battery optimization, split-tunneling configuration, and APK signature verification, see our Best VPNs for Android Torrenting.
Layer 2: Interface Binding — The Real Kill Switch (Critical)
This is the single most important configuration most torrent users skip, and it’s the difference between “mostly protected” and “actually protected.”
A standard VPN kill switch is reactive. It monitors the VPN tunnel and blocks traffic after it detects the connection has dropped. The problem is the gap — the 200–800 milliseconds between the tunnel failing and the kill switch activating. During that window, your torrent client can send packets through your real network interface, exposing your IP to every peer in the swarm. Copyright monitoring bots log IPs continuously, so even a sub-second exposure is enough.
Interface binding is proactive. You tell your torrent client to only use the VPN’s network adapter. It physically cannot communicate through any other interface. If the VPN drops, the adapter disappears, and the torrent client sees no network at all. There is no gap, no race condition, no timing vulnerability. Traffic either goes through the VPN or it doesn’t go at all.
How to Bind qBittorrent to Your VPN
Step 1: Identify your VPN’s network interface name.
Connect to your VPN first. Then find the adapter name:
- Windows: Open PowerShell and run
Get-NetAdapter | Where-Object {$_.Status -eq "Up"}. Look for the VPN adapter — it will be named something likeProtonVPN TUN,NordLynx,Wintun, orTAP-Windows Adapter. - macOS: Open Terminal and run
ifconfig. Look forutun3,utun4, or similar — the adapter that appeared after VPN connection. - Linux: Run
ip link show. Look fortun0(OpenVPN),wg0(WireGuard), orproton0(ProtonVPN).
Step 2: Set the binding in qBittorrent.
Go to Tools → Options → Advanced (or Preferences → Advanced on macOS). Find the “Network Interface” dropdown. Select the VPN adapter name you identified in Step 1.
Leave “Optional IP address to bind to” at its default (“All addresses” or “All IPv4 addresses”).
Click Apply, then OK. Restart qBittorrent.
Step 3: Verify with the Total Failure Test (see the dedicated section below).
Important caveat — dynamic interface names: Some WireGuard implementations generate a new interface name (like utun3 one session, utun4 the next) every time you reconnect. If this happens, check your VPN app’s settings for a “Persistent TUN” or “Stable Adapter” option. ProtonVPN and NordVPN both create consistently named adapters on desktop. If your VPN doesn’t, you’ll need to verify the name each session before launching your torrent client.
📱 Android: The OS-Level Equivalent
Android doesn’t support per-app interface binding the way desktop torrent clients do. But since Android 8+, the OS provides a system-wide equivalent that achieves the same result:
Settings → Network & Internet → VPN → [your VPN app] → tap the gear icon ⚙️ → enable two toggles:
- “Always-on VPN” — Android will automatically connect the VPN on boot and reconnect after any interruption.
- “Block connections without VPN” — This is the critical one. It tells Android to drop all network traffic if the VPN tunnel is down. No app on your device — including your torrent client — can reach the internet without the VPN.
This is interface binding at the OS level. It’s actually more comprehensive than qBittorrent’s per-app binding because it covers every app on the device, not just your torrent client.
Note: Some battery optimization features (Samsung’s “Deep sleeping apps,” Xiaomi’s “Battery saver”) will kill VPN apps running in the background. Exempt your VPN from battery optimization: Settings → Apps → [VPN app] → Battery → Unrestricted. Without this, Android may kill the VPN while your screen is off, and with “Block connections without VPN” enabled, your phone will lose all internet until you manually reopen the VPN app.
For the complete interface binding walkthrough including Transmission and Deluge clients, plus firewall-level enforcement on Linux (iptables/nftables) and macOS (pf), see our VPN for Torrenting Survival Guide.
Layer 3: DNS Leak Protection — Sealing the Metadata Channel
You’ve encrypted your traffic and bound your torrent client to the VPN. But there’s a parallel channel that most users forget about: DNS queries.
Every time your torrent client contacts a tracker, resolves a peer’s hostname, or your browser navigates to a torrent site, your device sends a DNS query — a request that translates a domain name (like torrentgalaxy.to) into an IP address. If these queries go to your ISP’s DNS servers instead of your VPN’s DNS servers, your ISP sees a complete list of every tracker and torrent site you visit, even though the actual download traffic is encrypted inside the VPN tunnel.
This is called a DNS leak, and it happens more often than you’d expect. Common causes include: Windows resolving DNS through all available adapters simultaneously (a known behavior called “smart multi-homed name resolution”), manually configured DNS servers (like Google’s 8.8.8.8 or Cloudflare’s 1.1.1.1) that bypass the VPN tunnel, and IPv6 DNS queries routing outside the VPN on networks where the VPN only tunnels IPv4.
How to Test for DNS Leaks
- Connect to your VPN.
- Visit ipleak.net in your browser.
- Look at the “DNS Addresses” section.
✅ Correct result: All listed DNS servers belong to your VPN provider. You should see zero references to your ISP.
❌ Leak detected: You see your ISP’s DNS servers listed alongside or instead of the VPN’s. This means your ISP can see which domains you’re resolving — effectively telling them which torrent sites and trackers you’re using.
How to Fix DNS Leaks
Use your VPN’s built-in DNS. Most quality VPN apps route DNS through the tunnel automatically. In ProtonVPN: Settings → Connection → DNS leak protection → ON (typically on by default). In NordVPN: Settings → Advanced → Custom DNS → disabled (let NordVPN handle DNS).
Disable smart multi-homed name resolution on Windows. Open PowerShell as admin and run:
Set-DnsClientGlobalSetting -UseDevolution $false
Or use Group Policy: Computer Configuration → Administrative Templates → Network → DNS Client → Turn off smart multi-homed name resolution → Enabled.
On Android: Set Private DNS to your VPN’s resolver. Settings → Network & Internet → Private DNS → Private DNS provider hostname (e.g., dns.quad9.net as a fallback, or leave on “Automatic” if your VPN app handles it).
Block IPv6 if your VPN doesn’t tunnel it. Many VPNs only route IPv4 traffic. If your network has IPv6 enabled, DNS queries can route outside the tunnel through IPv6. Check: visit test-ipv6.com with VPN active. If it shows a different IPv6 address than your VPN’s, disable IPv6 on your network adapter or enable your VPN’s IPv6 leak protection setting. (ProtonVPN and Mullvad both tunnel IPv6.)
Layer 4: WebRTC Leak Protection — Closing the Browser Backdoor
WebRTC (Web Real-Time Communication) is a browser technology designed for video calls and peer-to-peer file sharing directly in the browser. It’s built into Chrome, Firefox, Edge, and Opera by default. The problem: WebRTC uses STUN/TURN protocols that can reveal your real local and public IP addresses to any website you visit — even when a VPN is active.
This matters for torrenting because you browse torrent sites in your browser. If a malicious ad or script on a torrent site queries your WebRTC interfaces, it can extract your real IP address despite your VPN being connected. This isn’t theoretical — it’s one of the most common leak vectors documented in VPN leak testing.
How to Test for WebRTC Leaks
- Connect to your VPN.
- Visit browserleaks.com/webrtc.
- Look at the IP addresses listed.
✅ Correct result: You see only your VPN’s IP address, or “n/a” for local addresses.
❌ Leak detected: You see your real public IP or your local network IP (like 192.168.x.x or 10.x.x.x). The local IP alone reveals your network configuration; the public IP completely bypasses your VPN.
How to Fix WebRTC Leaks
Firefox: Type about:config in the address bar, search for media.peerconnection.enabled, and set it to false. This completely disables WebRTC.
Chrome/Edge: Install uBlock Origin and enable it via Settings → Privacy → Prevent WebRTC from leaking local IP addresses. Chrome doesn’t have a native toggle. Alternatively, install Google’s WebRTC Network Limiter extension.
Brave: Go to Settings → Privacy and security → WebRTC IP handling policy → Disable non-proxied UDP. Brave is the only Chromium-based browser with a native WebRTC control.
VPN app: Some VPN desktop apps include WebRTC protection. ProtonVPN’s browser extension blocks WebRTC leaks. NordVPN’s Threat Protection includes WebRTC blocking. Check your VPN’s settings for a WebRTC protection toggle.
Layer 5: Port Forwarding — Speed Without Exposure
Port forwarding isn’t a privacy layer — it’s a performance layer that many users misconfigure in ways that compromise their privacy. Including it here because doing it correctly through your VPN is part of the anonymous torrenting stack.
The Problem: NAT and CGNAT
By default, your VPN places you behind its NAT (Network Address Translation). Outgoing connections work fine — you can connect to peers and download from them. But incoming connections are blocked. Other peers trying to connect to you to request pieces you’re seeding get rejected by the VPN’s firewall.
The result: slower peer discovery, lower upload speeds, worse seeding ratios, and “partially connected” status on many trackers.
This problem compounds if your ISP also uses Carrier-Grade NAT (CGNAT) — a practice where ISPs assign multiple customers the same public IP address to conserve IPv4 space. CGNAT is increasingly common in 2026, especially on mobile networks and newer fiber ISPs. Under CGNAT, you’re behind two layers of NAT: your ISP’s and your VPN’s. Without port forwarding, incoming peer connections are essentially impossible, and even some outgoing connections may fail. Torrents can stall completely or download at a fraction of their potential speed.
If you’re seeing unusually slow torrent speeds or persistent “stalled” status even with well-seeded torrents, CGNAT may be the culprit. VPN port forwarding solves both the VPN’s NAT and your ISP’s CGNAT simultaneously — the VPN opens a direct path through both layers to your device.
The Solution: VPN-Based Port Forwarding
Some VPNs let you open a specific port on their server that routes incoming traffic directly to your device through the encrypted tunnel. This allows incoming peer connections without exposing your real IP.
VPNs that support port forwarding:
| VPN | Ports Available | Configuration | Notes |
|---|---|---|---|
| ProtonVPN | Up to 5 | Native app toggle (all platforms) | P2P servers marked with ↔ icon |
| PIA | 1 (random) | Settings → Network | Port changes on reconnection |
| AirVPN | Up to 20 | Web panel configuration | Most flexible option |
| Mullvad | ❌ Removed (2023) | N/A | Removed due to abuse concerns |
| NordVPN | ❌ None | N/A | — |
| ExpressVPN | ❌ None | N/A | — |
| Surfshark | ❌ None | N/A | — |
How to Configure It Safely
- Enable port forwarding in your VPN app.
- Connect to a P2P-optimized server (in ProtonVPN, look for the ↔ icon).
- Note the assigned port number (ProtonVPN displays it in the app dashboard).
- In qBittorrent: Tools → Options → Connection → Listening Port → enter the port number.
- Disable UPnP and NAT-PMP in the same Connection settings screen. This is critical — these protocols attempt to automatically open ports on your router, which can bypass the VPN tunnel and expose your real IP address to peers. When using VPN port forwarding, you want the torrent client to use only the VPN’s forwarded port.
A note on visibility: Port forwarding makes you “connectable” — meaning more peers can initiate connections to you. This improves speed and seeding ratio, but it also means more peers know the VPN port that routes to your device. This is not a privacy risk in practice because those peers only see your VPN’s IP address, and the port is assigned by the VPN server (not your real device). But it’s worth understanding: port forwarding trades a marginal increase in visibility for a significant increase in speed and connectivity.
For the detailed port forwarding setup with ProtonVPN (including Android), see our VPN for Torrenting Survival Guide.
Layer 6: Browser Hardening — Protecting Your Browsing Session
Your torrent client isn’t the only attack surface. Your browser — which you use to visit TorrentGalaxy, copy magnet links, and browse tracker forums — is exposed to malicious ads, tracking scripts, crypto miners, and phishing attempts. Hardening your browser is the final layer of the anonymous torrenting stack.
DNS-Level Ad and Malware Blocking
Most quality VPNs include DNS-level content filtering that blocks known malicious domains before your browser can connect to them:
- ProtonVPN NetShield — three modes: Block malware, Block malware + ads, Block malware + ads + trackers.
- NordVPN Threat Protection Lite — blocks ads, trackers, and malicious sites at the DNS level.
- PIA MACE — DNS-level blocking of ads, trackers, and malware.
- Surfshark CleanWeb — similar DNS-level filtering.
Enable whichever your VPN provides. It operates at the network level, meaning it protects all apps on your device — not just your browser.
Browser-Level Blocking with uBlock Origin
DNS-level blocking catches domain-level threats, but it can’t block inline malicious JavaScript, specific page elements, or advanced tracking scripts embedded in otherwise legitimate pages. uBlock Origin handles the layer DNS blocking misses.
Install uBlock Origin from the official browser extension stores (available for Firefox, Chrome, Edge, Brave). Leave the default filter lists enabled — they cover most malicious ad networks. For torrent sites specifically, enable the additional filter list: uBlock Filters – Annoyances.
Use both DNS-level and browser-level blocking simultaneously. They protect different layers and complement each other with zero performance conflict.
Additional Browser Hygiene
Use a separate browser profile for torrenting. Most browsers support multiple profiles. Create one dedicated to visiting torrent sites — with uBlock Origin installed, WebRTC disabled, and no personal accounts logged in. This prevents cross-contamination between your torrenting activity and your personal browsing (email, banking, social media).
Never download .exe files from torrent site ads or pop-ups. Legitimate torrents are small .torrent files (under 1 MB) or magnet links that open directly in your torrent client. Any prompt to “download our custom player” or “install this codec” is malware. For detailed guidance on identifying malicious downloads, scanning files with VirusTotal, and sandboxing suspicious content, see our TorrentGalaxy Safety Guide.
The Pre-Session Checklist
Every time you sit down to torrent, run through this sequence before clicking a single magnet link. It takes 60 seconds and covers all six layers:
1. VPN connected to P2P server. Confirm the VPN app shows “Connected” and you’re on a server that supports P2P traffic. Use WireGuard protocol.
2. Interface binding set. Launch the torrent client after the VPN is connected. The adapter must exist before the client initializes.
3. Leak test passed. Visit ipleak.net and confirm: (a) your displayed IP is the VPN’s IP, not your real IP, (b) DNS servers belong to your VPN provider, (c) no WebRTC leak detected. Use ipleak.net’s Torrent Address Detection test — it provides a magnet link that, when loaded in your torrent client, reports which IP your client is using in the swarm.
4. DNS blocker active. NetShield, Threat Protection, MACE, or CleanWeb enabled in your VPN app.
5. uBlock Origin running. Check the extension icon in your browser — it should show a number (blocked elements count), not be greyed out.
6. Port forwarding configured (if available). VPN port forwarding enabled, assigned port entered in torrent client, UPnP/NAT-PMP disabled.
⚠️ The “Total Failure” Test
This is the most important test in this entire guide. Do it once after initial setup, and again after any VPN update, OS update, or configuration change. It takes 90 seconds and definitively proves whether your setup works.
- Connect your VPN and open your torrent client.
- Start downloading a well-seeded legal torrent (Ubuntu ISO, LibreOffice, or any Creative Commons file).
- Confirm it’s downloading at normal speed (the specific speed doesn’t matter — just that it’s active and peers are connected).
- Disconnect your VPN while the download is running. Don’t pause or close the torrent client — let it keep trying.
- Watch what happens.
✅ PASS: Download speed drops to 0.0 KiB/s within 5 seconds. All peers disconnect. Status shows “Stalled” or “No connection.” Your torrent client cannot reach the internet at all. This is the correct behavior — your setup is working.
❌ FAIL: Speed drops but doesn’t reach zero, or the torrent reconnects to peers after a brief pause. This means your real IP is being exposed. Go back to Layer 2 and verify the correct adapter is selected in qBittorrent’s Advanced settings, or confirm “Block connections without VPN” is enabled on Android.
- Reconnect your VPN. The download should resume automatically within 10–30 seconds as the tunnel re-establishes and peers reconnect.
If you pass this test, your setup is solid. An accidental VPN disconnection during a real download will produce the same behavior — total silence, zero leaked packets, automatic recovery on reconnection.
Common Mistakes That Break Your Protection
Even with all six layers configured, these specific errors can re-expose your identity:
Opening your torrent client before the VPN connects.
If qBittorrent launches before the VPN adapter exists, it may bind to your physical network interface and stay there — even if the VPN connects afterward. Always connect VPN first, then launch the torrent client.
Using free VPNs.
Free VPNs cannot sustainably absorb the bandwidth costs of P2P traffic. They monetize through data logging, ad injection, or selling your bandwidth as an exit node (the Hola case — your device becomes a proxy for other users). A free VPN is worse than no VPN: without a VPN, only peers in the swarm see your IP; with a malicious free VPN, the VPN company has a complete log of your activity tied to your email and payment information. Paid VPNs cost $2–3/month on annual plans. For the full breakdown, see our Best VPNs for Android.
Leaving UPnP/NAT-PMP enabled alongside VPN port forwarding.
These protocols tell your router to open ports directly, potentially routing traffic outside the VPN tunnel. When using VPN-based port forwarding, disable UPnP and NAT-PMP in your torrent client’s connection settings.
Ignoring IPv6.
If your VPN only tunnels IPv4 but your network has IPv6 enabled, your torrent client may make some connections over IPv6 — outside the VPN tunnel. Either disable IPv6 on your network adapter, or use a VPN that explicitly tunnels IPv6 traffic (ProtonVPN and Mullvad both do).
Using the same browser profile for torrenting and personal browsing.
If you’re logged into Google, Gmail, or social media in the same browser window where you visit torrent sites, those services can correlate your browsing patterns. Use a separate browser profile — or a separate browser entirely — for torrent-related browsing.
Trusting RARBG clones or YTS with real credentials.
RARBG shut down permanently on May 31, 2023. Every site using the RARBG name is a clone — they scrape cached databases and inject malicious ads, fake download buttons, and .exe payloads. YTS is a separate concern: a 2020 settlement revealed the site shared user IP addresses and email addresses with a copyright enforcement law firm. For a detailed breakdown of safe vs. dangerous torrent sites, see our Torrent Search Blueprint.
Advanced: Layering for Maximum Anonymity
For most users, the six layers above provide comprehensive protection. But if you’re in a high-risk environment (journalist protecting sources, resident of a country with aggressive surveillance, or simply want the strongest possible setup), here are additional measures:
VPN + SOCKS5 Proxy (Double Layer)
Some VPNs (NordVPN, PIA) offer SOCKS5 proxy addresses that you can configure inside your torrent client, in addition to running the VPN system-wide. This creates two layers: the VPN encrypts and tunnels all traffic at the OS level, and the SOCKS5 proxy adds a second IP mask specifically for torrent traffic.
A SOCKS5 proxy alone provides no encryption and no DNS leak protection. It’s only useful as a secondary layer on top of an active VPN. Never use a SOCKS5 proxy as your primary protection for torrenting. See our VPN for Torrenting Survival Guide for the full comparison.
Seedbox (Remote Downloading)
A seedbox is a dedicated server (usually rented monthly) that runs a torrent client on your behalf. You add torrents through a web interface, the seedbox downloads/seeds using its datacenter IP address, and you retrieve the completed files via HTTPS or SFTP. The seedbox’s IP appears in the swarm, not yours. However, you still need a VPN when connecting to the seedbox itself — the seedbox provider has your payment information and login IP.
I2P (Invisible Internet Project)
I2P is an anonymizing network layer designed specifically for P2P. Traffic is routed through multiple encrypted tunnels across a distributed network of volunteer nodes. The torrent client BiglyBT has native I2P integration, and a dedicated tracker (tracker2.postman.i2p) has operated inside I2P for over a decade.
The tradeoff is speed — I2P is significantly slower than a direct VPN connection. But it offers the strongest anonymity because there’s no central server, no company holding your account, and no single point of failure. I2P is censorship-proof in a way that VPN services fundamentally cannot be.
FAQs
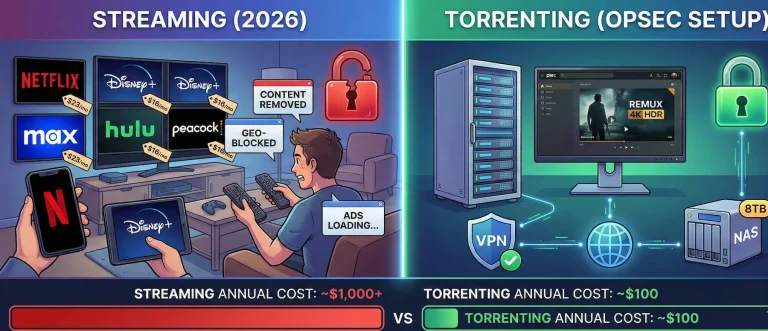
Torrenting itself is legal — BitTorrent is a legitimate file-sharing protocol used by Linux distributions, game companies, and academic institutions. What’s potentially illegal is downloading copyrighted content without authorization. A VPN doesn’t change the legality of what you download — it prevents third parties from identifying you through the swarm’s public peer list.
No. Tor is designed for low-bandwidth web browsing, not sustained data transfer. BitTorrent traffic over Tor is extremely slow, overloads the volunteer-run network, and critically, Tor doesn’t handle UDP traffic — which DHT and most peer connections use. UDP packets bypass the Tor circuit entirely, exposing your real IP. The Tor Project explicitly asks users not to torrent over Tor. Use a VPN.
How much does a VPN slow down torrenting?
With WireGuard on a server geographically close to you, expect a 3–8% speed reduction compared to your naked connection. This is far less than the throttling most ISPs apply to unencrypted BitTorrent traffic, meaning a VPN often increases effective torrent speed by defeating DPI-based throttling.
Do I need a VPN on private trackers?
Yes. Private trackers require registration and enforce ratio requirements, but your IP address is still visible to every peer in the swarm. The tracker itself also logs your IP. A private tracker’s “invite-only” status doesn’t prevent monitoring companies from obtaining invites or a compromised tracker database from leaking your IP history.
What is CGNAT and why does it affect my torrents?
Carrier-Grade NAT (CGNAT) is when your ISP puts multiple customers behind a single public IP address. It’s increasingly common on mobile carriers and newer ISPs. Under CGNAT, incoming peer connections to your device are blocked at the ISP level — before your traffic even reaches your VPN. The result is slower peer discovery and potential stalling. VPN port forwarding (Layer 5) solves this by providing a direct path through both NAT layers.
How do I know if my VPN has been compromised?
Run the full leak test at ipleak.net periodically — check IP, DNS, WebRTC, and the torrent detection test. If any show your real IP or ISP’s DNS servers, something has changed. Also watch for: the VPN provider changing its logging policy, being acquired by a company in a Five Eyes jurisdiction, or failing to publish regular independent audit results.
What’s the difference between a kill switch and interface binding?
A kill switch is reactive — it detects VPN disconnection and blocks traffic after the fact. Interface binding is proactive — it restricts your torrent client to only use the VPN’s network adapter, making it physically impossible to communicate through any other interface. Binding is more reliable because there’s no gap between disconnection and protection. Use both: binding for your torrent client, kill switch for everything else.
The TorrentGalaxy OPSEC Series
This pillar guide covers the strategic overview. For detailed walkthroughs of each component, see the full series:
- Why You Need a VPN for Torrenting: The 2026 Survival Guide — Deep dive into swarm exposure mechanics, encryption protocols, interface binding walkthrough, port forwarding setup, VPN vs. SOCKS5 comparison.
- Best VPNs for Android Torrenting (2026) — Android-specific VPN reviews, battery optimization, Always-on VPN setup, split-tunneling, APK signature verification, post-quantum encryption status.
- The 2026 Torrent Search Blueprint — Three-layer search architecture (Direct Indexers → Meta-Search → DHT Crawlers), dead site warnings (RARBG, YTS), Jackett/Prowlarr automation setup.
- Is TorrentGalaxy Safe? The Complete Safety Guide — Domain verification, uploader reputation system, file scanning with VirusTotal, sandboxing suspicious downloads, ad-blocker configuration.
- TorrentGalaxy Proxy List with Safety Ratings — Verified proxy and mirror list with real-time status, safety ratings, and connection instructions.
- TorrentGalaxy Power User Guide — DNS-over-HTTPS (DoH), Encrypted Client Hello (ECH), Tor access, and advanced proxy-free browsing methods.
TorrentGalaxy does not host copyrighted content. This guide covers operational security practices for BitTorrent protocol usage. Always respect copyright laws in your jurisdiction.